One Revenue Stream May No Longer Be Enough
Selling software used to be more straightforward. You had a product, you set a price, and someone paid it - a perpetual license, a yearly subscription, a one-off invoice. Both sides knew what the deal was.
The AI-Driven Transformation of Enterprise Software Licensing: From Seats to Tokens
Enterprise software licensing is undergoing its most significant transformation since the shift to cloud computing, driven by the rapid adoption of Artificial Intelligence across business operations. As companies race to monetize AI investments, traditional seat-based licensing models are giving way to consumption-based pricing structures that align costs with actual usage, particularly token consumption and API calls.
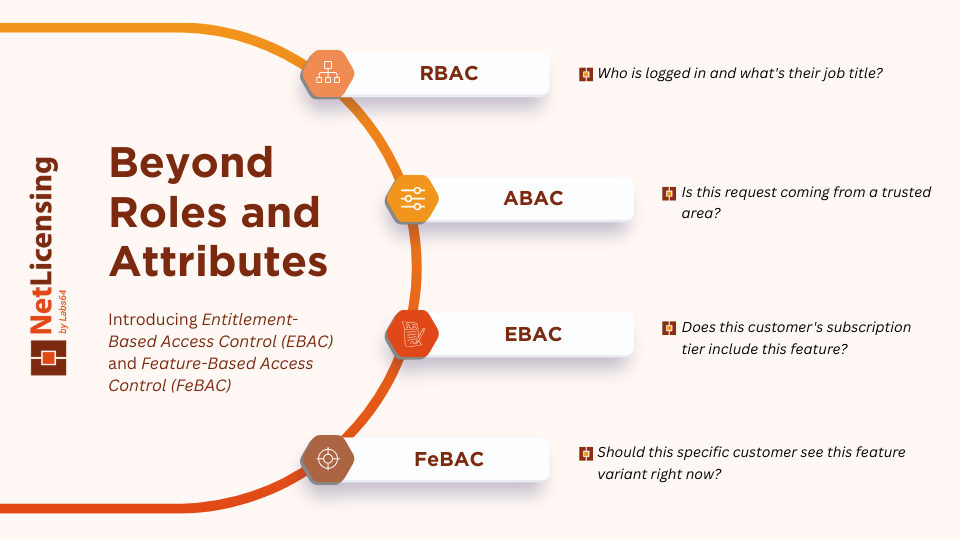
Beyond Roles and Attributes: Introducing Entitlement-Based Access Control (EBAC) and Feature-Based Access Control (FeBAC)
Access control has evolved significantly over the past two decades. Organizations started with simple Role-Based Access Control (RBAC), moved to more flexible Attribute-Based Access Control (ABAC), and now face a new challenge: managing business entitlements alongside security permissions. Enter Entitlement-Based Access Control (EBAC) and Feature-Based Access Control (FeBAC) - two emerging paradigms that extend the traditional authorization frameworks to handle product licensing, subscription tiers, and feature accessibility.
Software License Entitlements and Monetization - Market Analysis Report 2026
The global software license management market has evolved into a sophisticated ecosystem where traditional perpetual licensing gives way to dynamic, consumption-driven models. Valued at USD 3.67 billion in 2026, the market is projected to reach USD 18.1 billion by 2037, representing a compound annual growth rate (CAGR) of 13.7%1. This expansion is fundamentally reshaping how software vendors monetize products and how enterprises manage their digital assets.
From Payments to Licensing - Why NetLicensing Plus Stripe Is a Perfect Match
In the fast-paced world of software development, efficiently selling and managing software licenses is critical to business success. While Stripe has become a go-to solution for handling payments, it falls short when it comes to managing software licenses. This is where NetLicensing comes into play. By integrating NetLicensing with Stripe, businesses can unlock a powerful combination of payment processing and advanced licensing management. In this article, we’ll explore why this integration is more beneficial than using Stripe alone and how it can transform your software licensing operations.
Labs64 NetLicensing Cyber Weeks 2025 - Unlock Maximum Value and Innovation!
Join us for our biggest and most exclusive event ever - Cyber Weeks 2025, running from November 28 to December 8, 2025.